Blue Team Labs Online - Heaven

One fine day, watching your miserable life. A supreme power dropped a heavenly executable on your Desktop.
Reverse Engineering
Tags: x64Dbg dnSpy HxD DiE rtdump.py T1204.002 T1071.001
Scenario One fine day, watching your miserable life. A supreme power dropped a heavenly executable on your Desktop. Please find the dropper and Heaven.exe on the Desktop. Find the way to Heaven by answering the questions.
Environment Awareness
Evidence & Tool Discovery
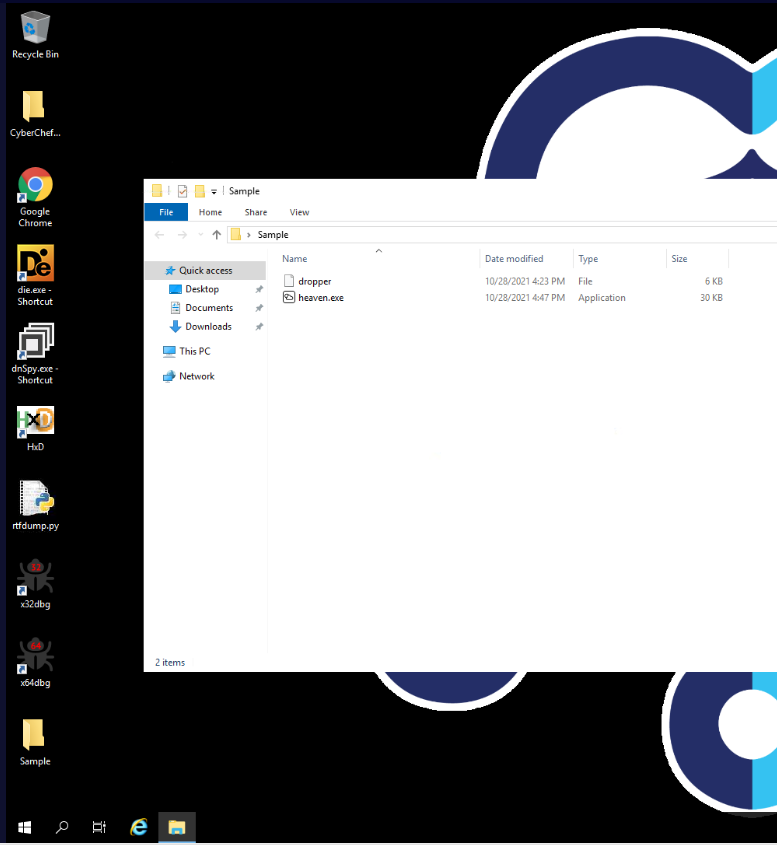
We have 2 samples within Sample folder located on the Desktop here and after reviewing these filename, dropper seem to be a dropper that will be used to drop heaven.exe on the target system.
we also have several tools that can be used for malware analysis such as - Detect It Easy : A tool use for file type identification - dnSpy : .NET decompiler - HxD : Hex editor - rtfdump : Tool from Didier Stevens suite that can be used to analyze RTF file - x32dbg/x64dbg : Debugger for PE32 executable files - CyberChef : The Cyber Swiss Army Knife - a web app for encryption, encoding, compression and data analysis.
Now lets dive it!
Investigation
Q1) Submit the File Signature of dropper in Hex format (Format: XX XX XX XX XX XX)
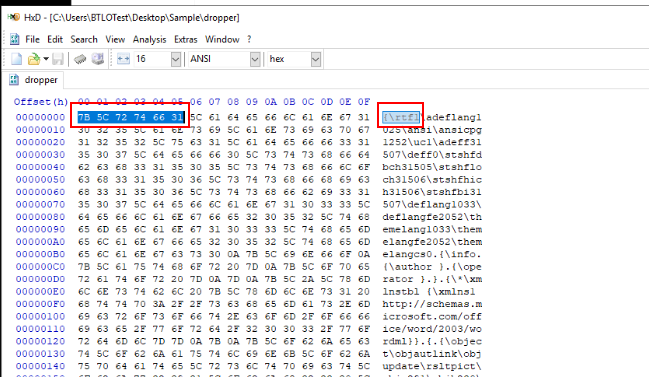
We can use HxD to open dropper file which we can see that this file is the RTF file and we can copy these part to answer this question.
Answer
7B 5C 72 74 66 31Q2) Submit the URL from where dropper is downloading the malicious executable (Format: http://domain.tld/path/to/file.exe)
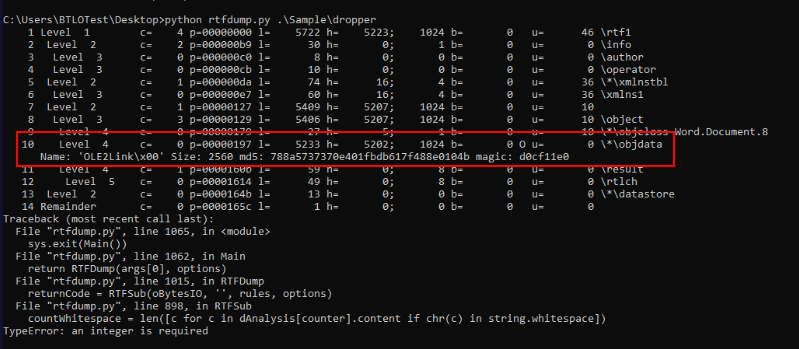
Its time to utiized rtfdump, we can just run it with the dropper file without any argument to let it analyze objects within this file which we can see that object 10 contains objdata with a size of 2560 bytes so lets take a look what inside of it
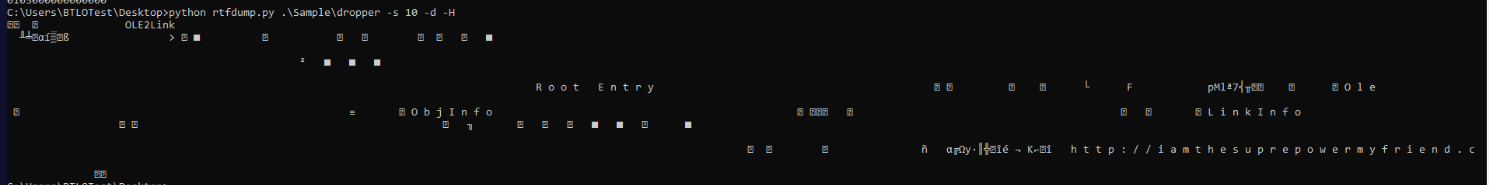
We can use -s 10 to specify object 10, -d for dump and -H for hex decode which we can see some a suspicious domain which in this object
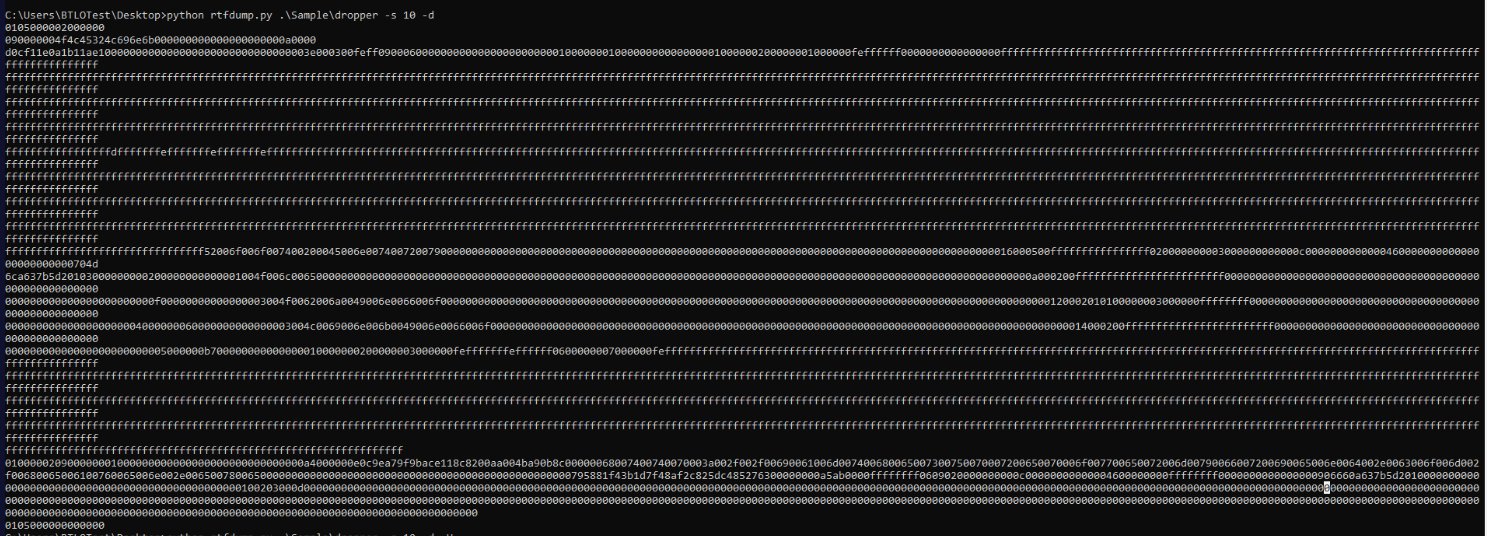
So lets remove -H and just dump as it hex and convert it in CyberChef which will make copy and paste a little bit easier
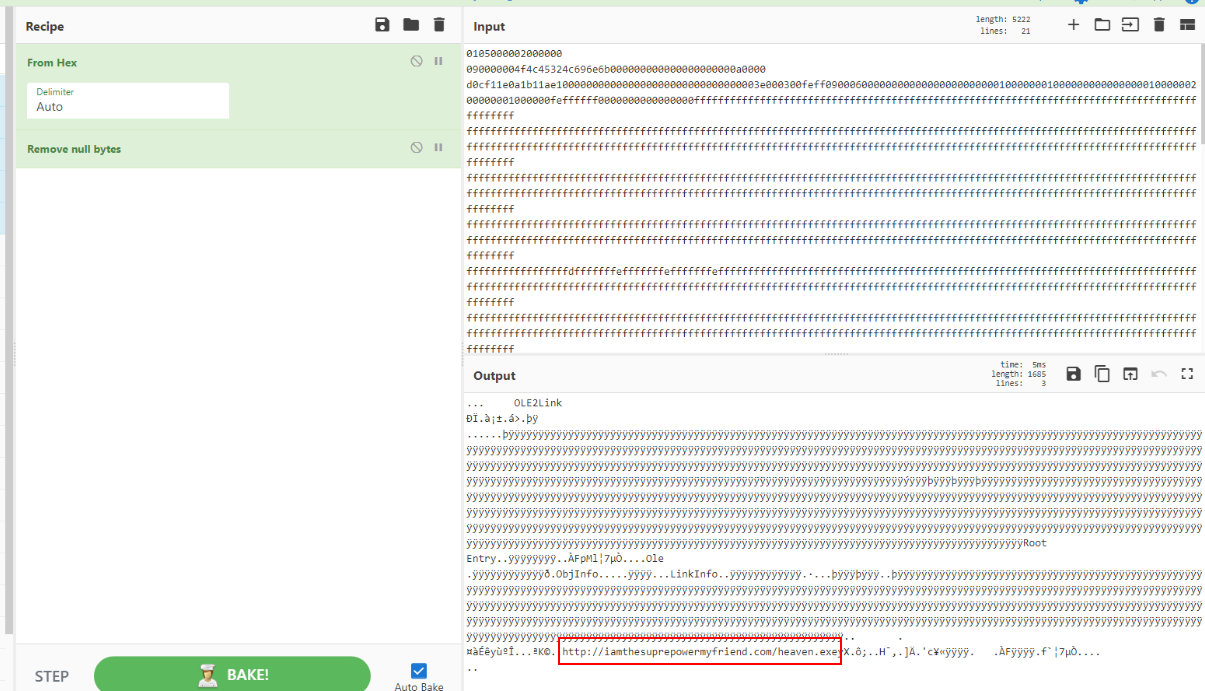
Then we will finally have the domain that this dropper will attempt to make a connection and download second payload (heaven.exe) here
Answer
http://iamthesuprepowermyfriend.com/heaven.exeQ3) According to DiE, what is the name of the linker used in heaven.exe? (Format: Format: string(x.x)[string])
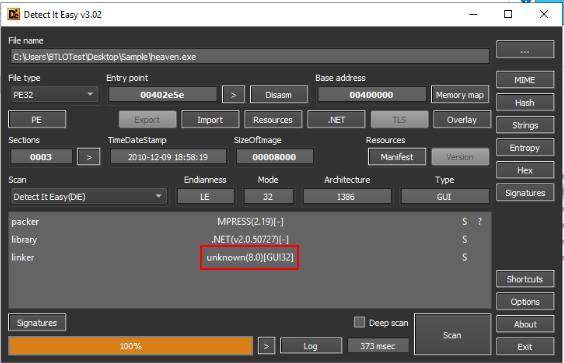
Now we can use DiE or Detect It Easy to identify the file type of second payload which we can see that it could not recognize known linker for this executable.
Answer
unknown(8.0)[GUI32]Q4) Submit the BaseAddress and EntryPoint of heaven.exe (Format: BaseAddress, AddressOfEntryPoint)
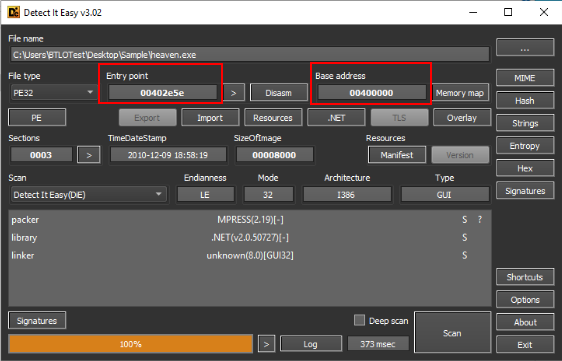
We can see both Entry Point and Base Address of this executable right here.
Answer
00400000, 00402e5eQ5) Submit the name of the software framework used by the malware author to create heaven.exe (Format: SoftwareFramework)
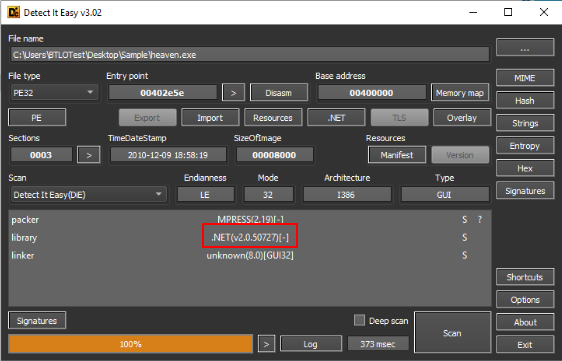
Take a look at Library which we can see that this malware was developed using .NET framework and one more thing to notice is its also packed with MPRESS so we will have to unpack it first before analyze it properly.
Answer
.NETQ6) What is the C2 IP that Heaven.exe will communicate with? (Format: X.X.X.X)
Lets following this gold mine to unpack MPRESS .NET executable via dnSpy
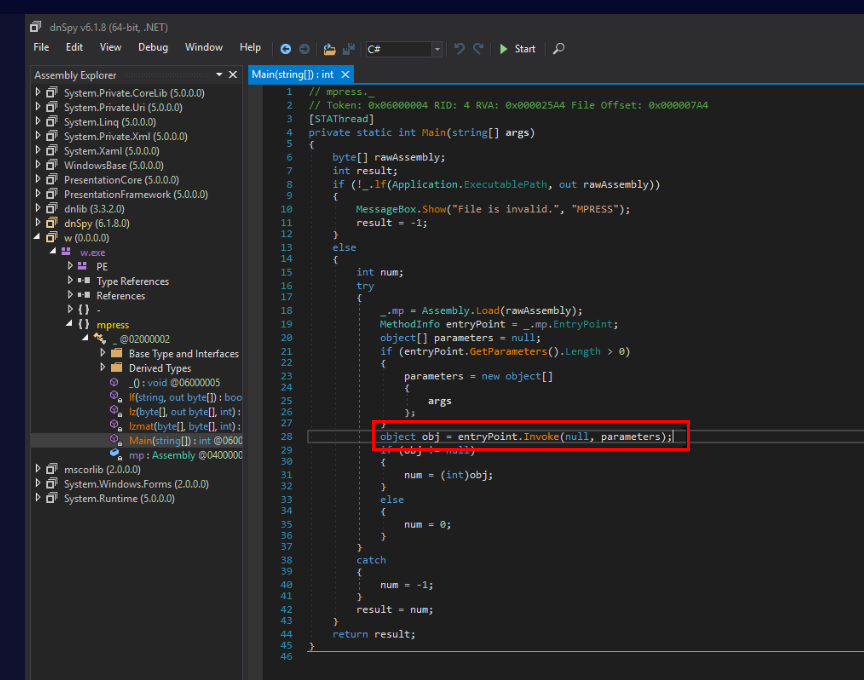
First we have to find where the entrypoint will be invoked and we should be able to see this on line 28 inside Main()
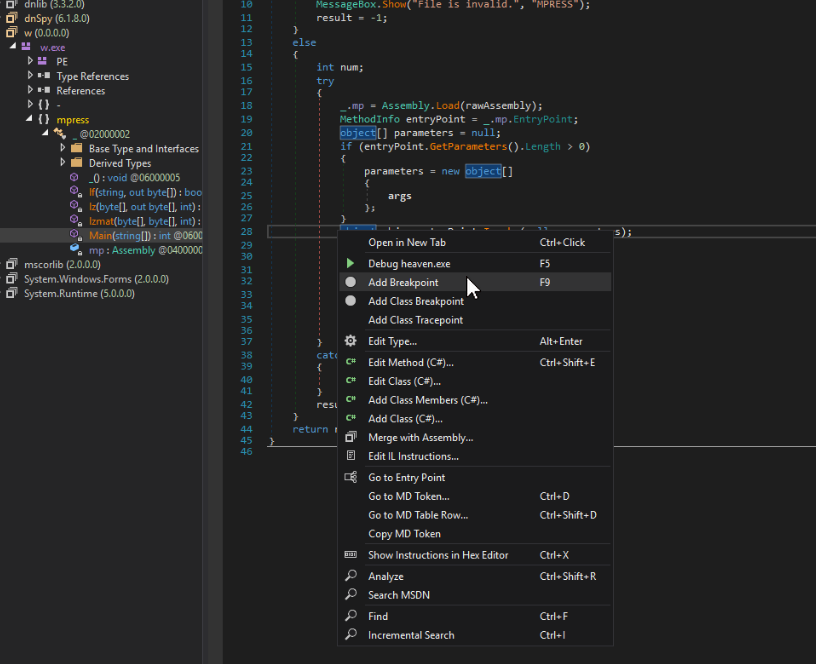
Lets add breakpoint here.
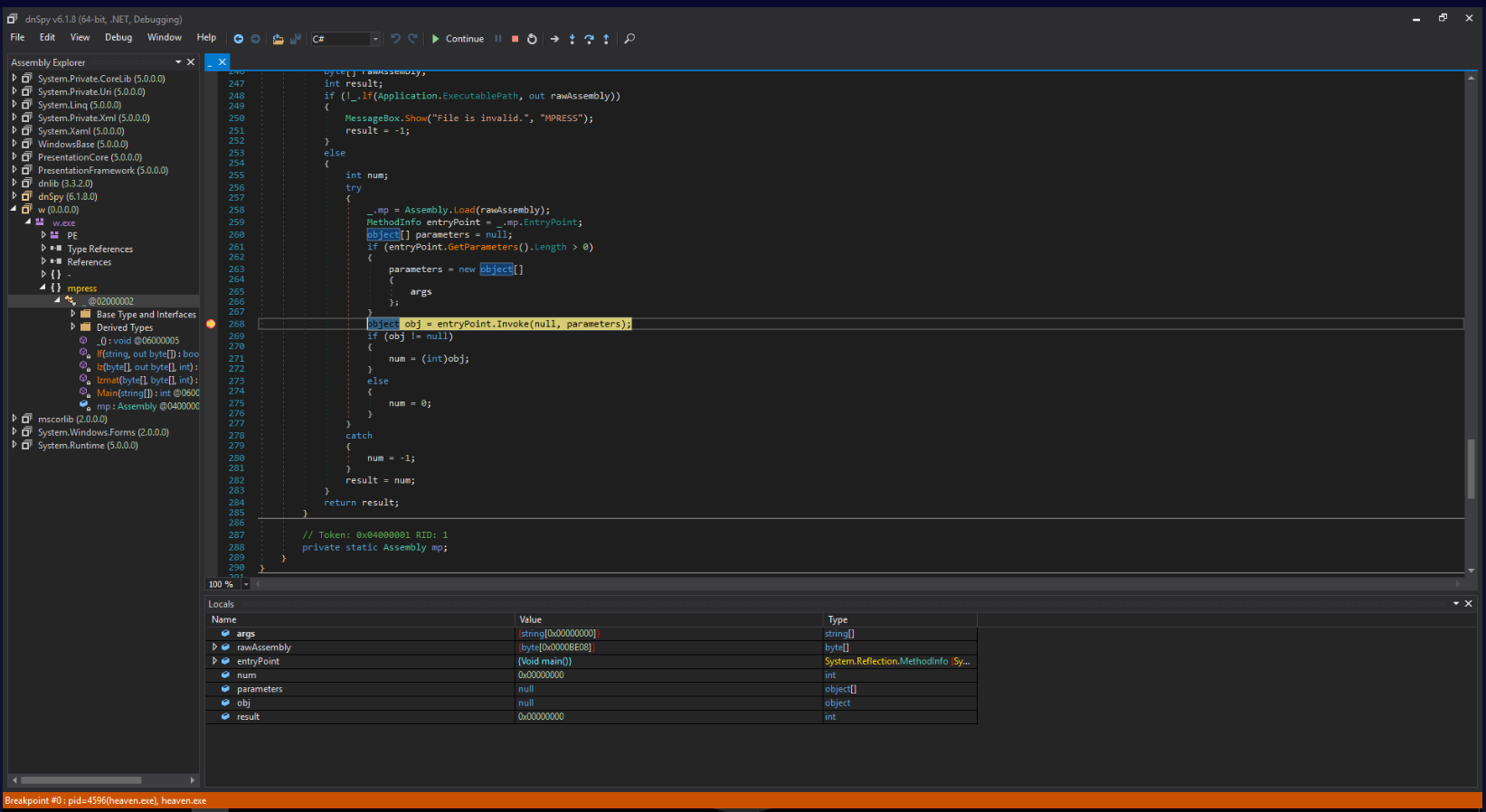
Now we can debug this file and it will stop at the breakpoint we just added.
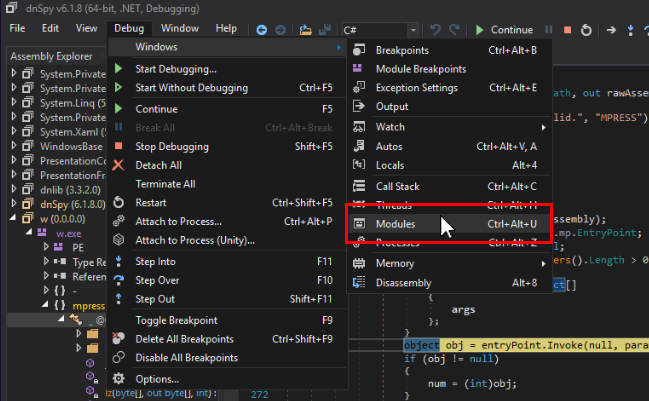
Now lets open Modules tab.
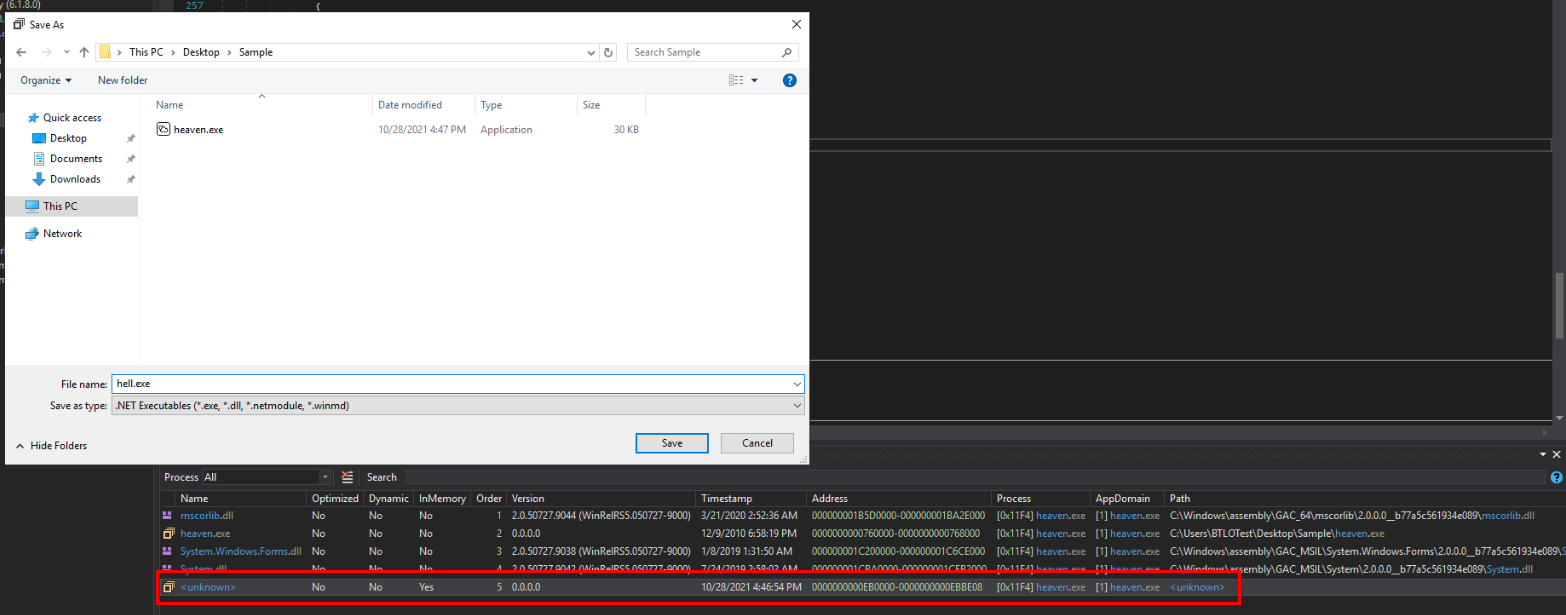
Save this unknown part which is unpacked executable file as a new file.
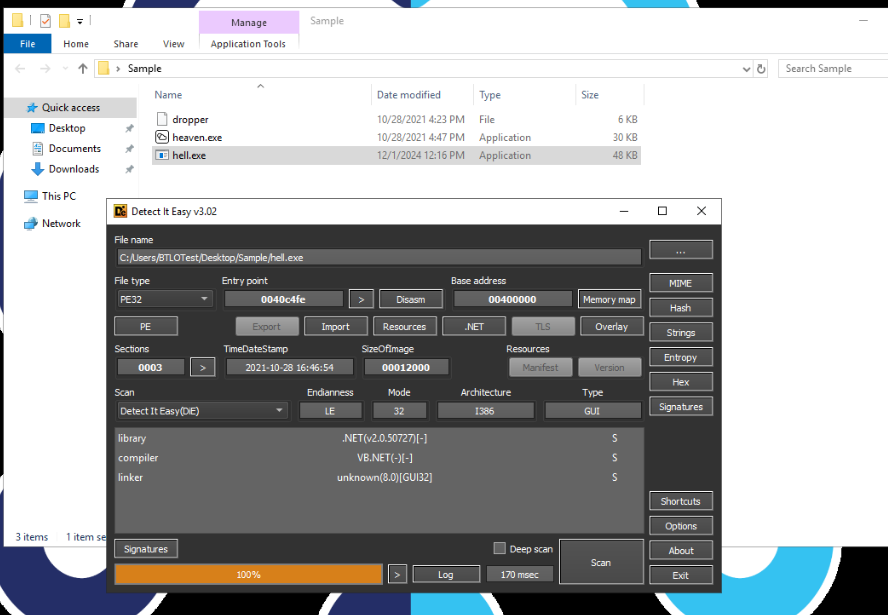
Now we can see that there is no more packer then we should be able to decompiled it on dnSpy and find out the C2 IP address easily.
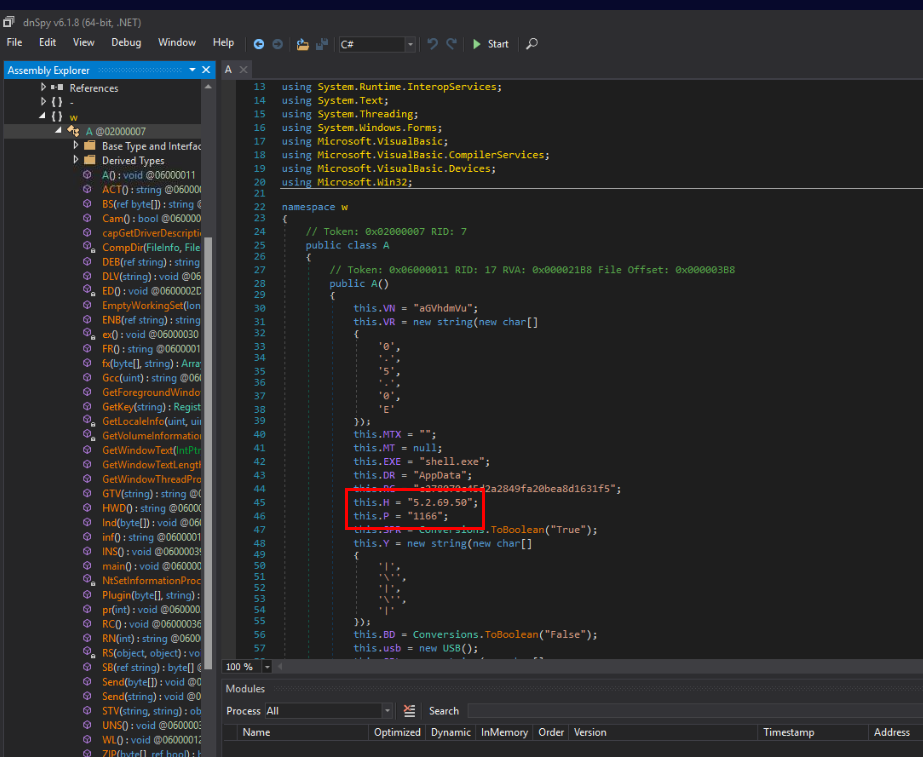
We can see that under A class, there is an A function that declares many variables including the IP address and port of C2 right here.
Answer
5.2.69.50 https://blueteamlabs.online/achievement/share/52929/82
https://blueteamlabs.online/achievement/share/52929/82